Ida Pro Reverse Engineering
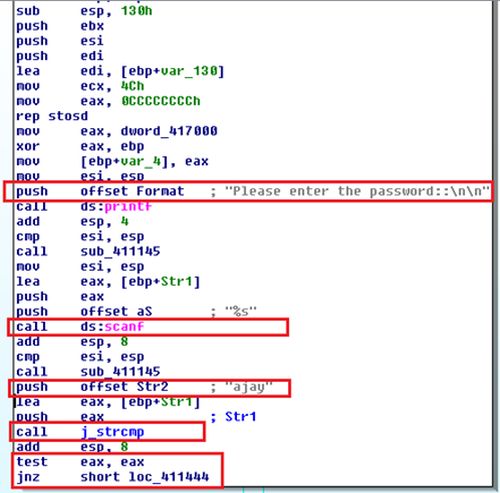
Mar 08, 2012 How to Reverse Engineer with IDA Pro Disassembler Part1 - Duration: 19:56. Reverse Engineering 101 ( Using A Hex Editor To Find Passwords ). This chapter discusses the debugging basics. Debugging is the act of locating bugs in software. Debuggers are essential tool in the reverse engineer's toolbox.
Reverse Engineering Ida Pro Pdf

Ida Pro Reverse Engineering Debugging
If you know the base, you can 'force' the display of the offset by using the ' Offset (user-defined)' command (Ctrl+R by default). You can then specify the base from which the offset have to be calculated, and IDA will basically add and substract the base, so it'll give: RVA 0x1234 with BaseAddress 0x400000 = (loc401234 - 0x400000) Unfortunately, there is no easy way to differentiate a small constant and a RVA, beside maybe looking if the destination already has a name, but that's error-prone since the only reference to that location could be the very same RVA you're manipulating. Either manual inspection of each value or custom-made heuristics would be my best guess.